Zero Doctrine™ Adoption ModelZero Doctrine™ Authority Model
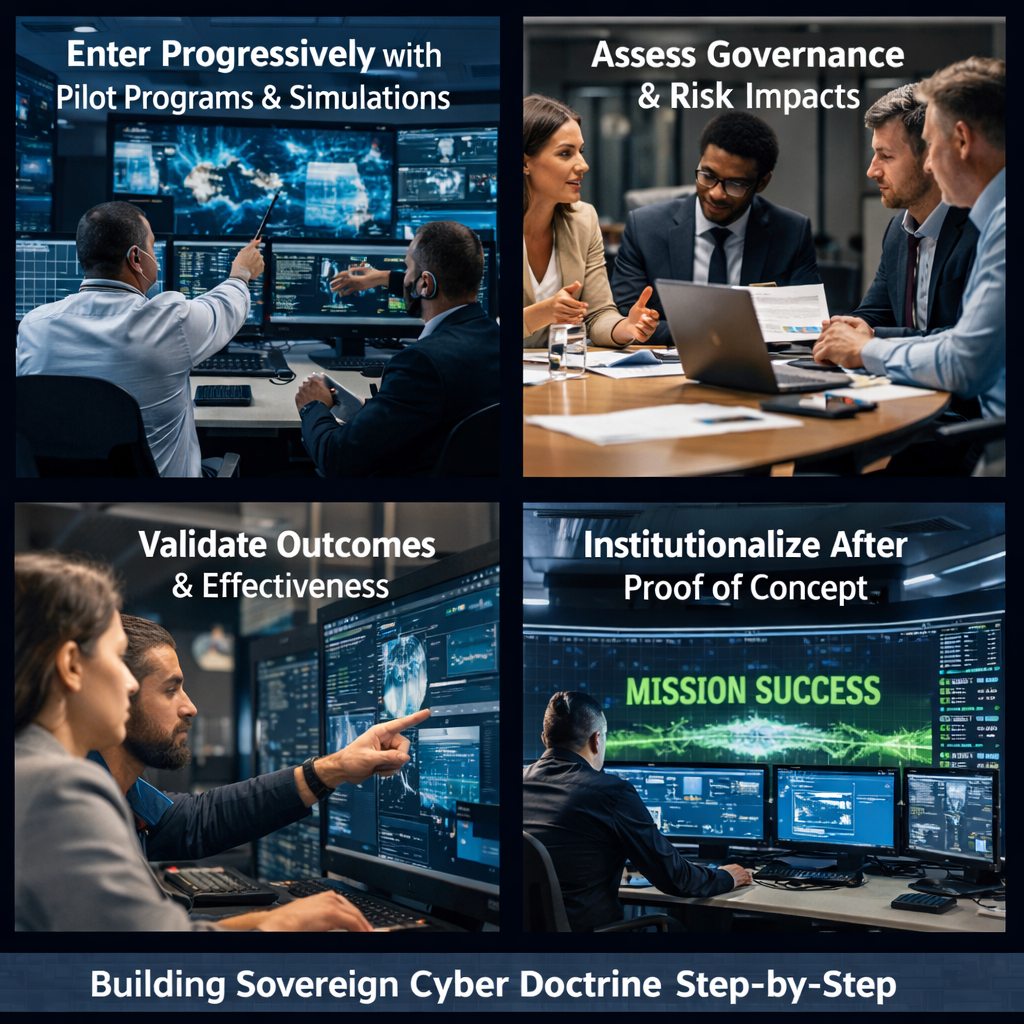
It is designed to be entered progressively, validated through simulation, and institutionalized only after proof.
Most organizations do not begin with architectural overhaul or enterprise-wide mandates.
They begin by testing doctrinal readiness, understanding governance implications, and validating outcomes before commitment.
This library explains how that process works.
Adoption Is Tiered, Not Monolithic
Adoption Tiers
• Tier 0 — Orientation
• Doctrine briefings and conceptual grounding
• No operational or architectural change
• Tier 1 — Validation (SecureTrain™)
• Sovereign-grade simulation to test readiness under pressure
• No infrastructure rebuild
• No long-term commitment
• Tier 2 — Operational Pilot
• Limited-scope enclave or mission domain
• Governance and doctrine applied where it matters most

• Tier 3 — Institutional Adoption
• Doctrine becomes the operating standard
• Licensing, auditing, and recurring readiness exercises
• Tier 4 — Sovereign / National Adoption
• Doctrine embedded as mandatory posture
• Partner certification and sector-wide enforcement
Most organizations operate comfortably in Tiers 1–3.
SecureTrain™: The Entry Point for Most Organizations
It is not training in the traditional sense.
It is doctrinal simulation designed to prove how systems, people, and governance perform under real operational pressure.
SecureTrain™ allows organizations to:
• Validate readiness without architectural disruption
• Identify governance and decision gaps before incidents occur
• Measure outcomes without committing to full adoption
For many organizations, SecureTrain™ is both the starting point and the decision gate.

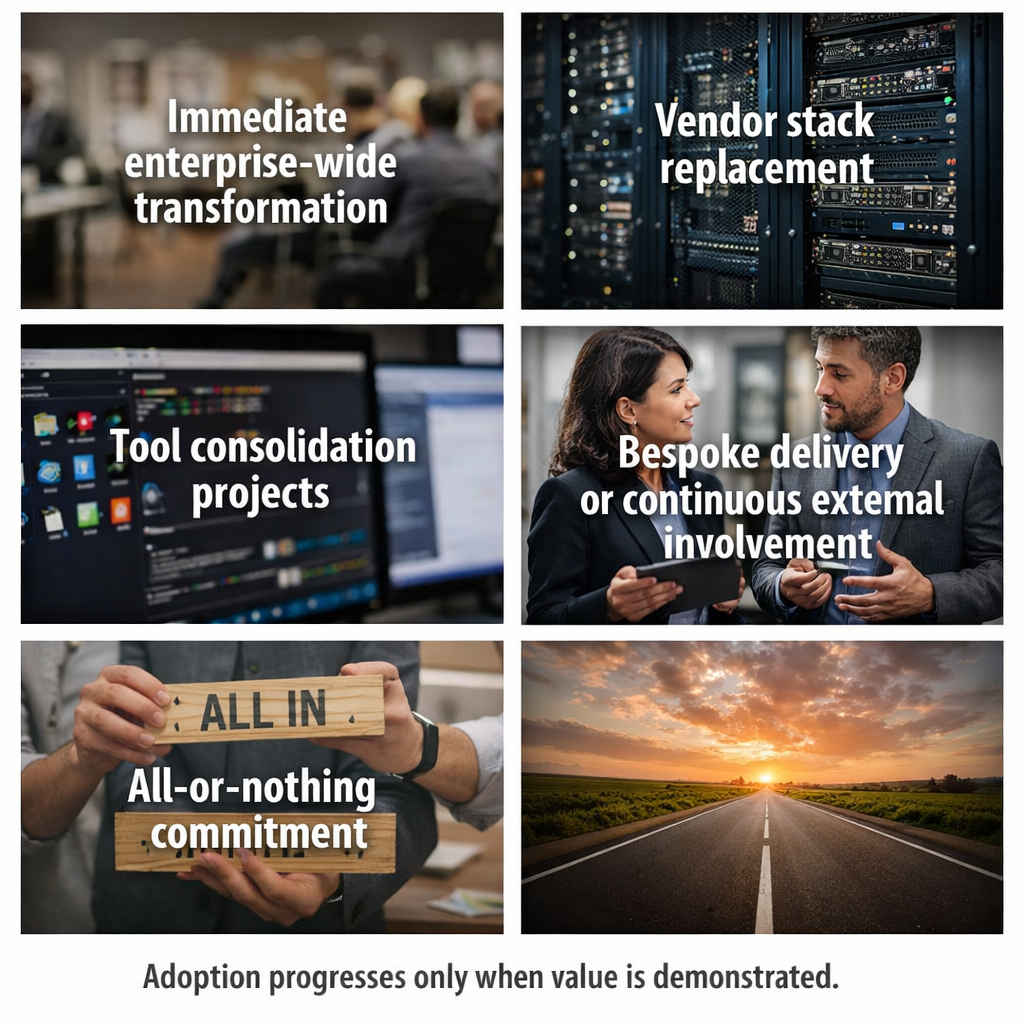
What Adoption Does Not Require
• Immediate enterprise-wide transformation
• Vendor stack replacement
• Tool consolidation projects
• Bespoke delivery or continuous external involvement
• All-or-nothing commitment
Adoption progresses only when value is demonstrated.
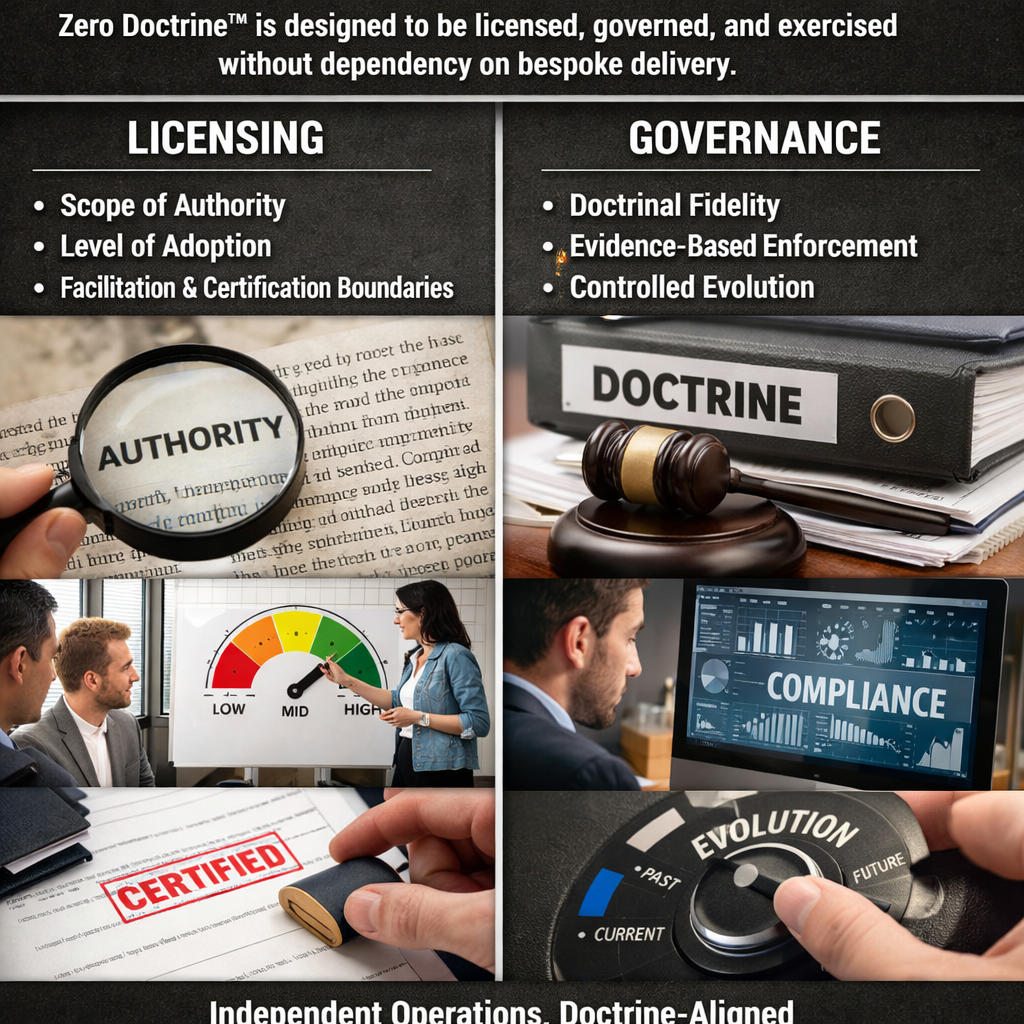
Licensing and Governance Enable Independent Execution
Licensing defines:
• Scope of authority
• Level of adoption
• Facilitation and certification boundaries
Governance ensures:
• Doctrinal fidelity
• Evidence-based enforcement
• Controlled evolution over time
This structure allows organizations to operate independently while remaining doctrine-aligned.
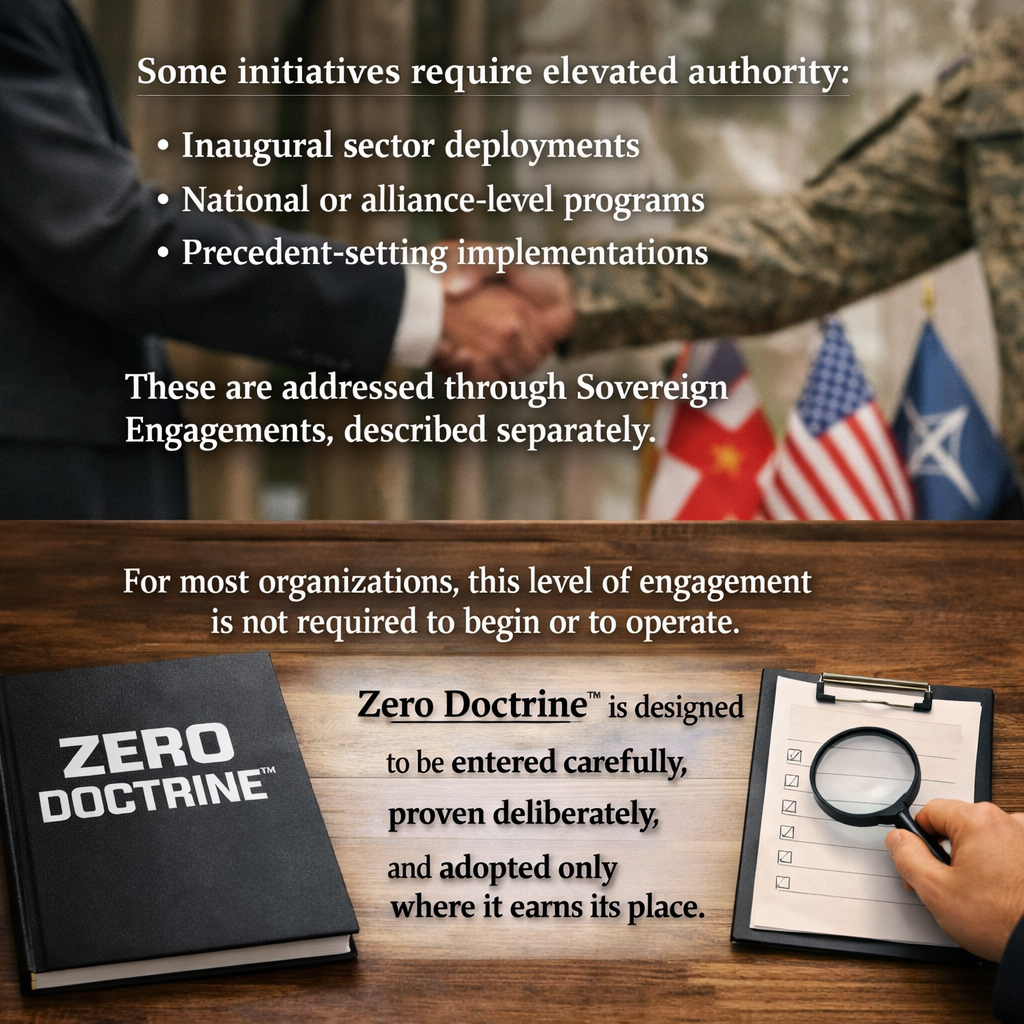
When Deeper Engagement Occurs
• Inaugural sector deployments
• National or alliance-level programs
• Precedent-setting implementations
These are addressed through Sovereign Engagements, described separately.
For most organizations, this level of engagement is not required to begin or to operate.
Zero Doctrine™ is designed to be entered carefully, proven deliberately, and adopted only where it earns its place.